Understanding how to recognize SQL injection techniques is crucial for anyone managing websites or databases today. SQL injection remains one of the most common threats in 2026, putting data, customers, and entire businesses at risk.
If you run a tech blog, manage a data-driven website, or work in information security, you need the most up-to-date guidance. In this article, you will learn how to spot these attacks with real examples and clear steps.
Whether you design web forms, write backend code, or handle client data, knowing the signs of SQL injection helps prevent breaches. Read on for hands-on advice and industry-backed solutions tailored for digital professionals and business owners in the ismartfeed.com community.
Understanding SQL Injection: What It Is and Why It Matters
Before learning how to recognize SQL injection techniques, it’s important to know what SQL injection (SQLi) means. SQL injection is when an attacker adds harmful SQL code to input fields, URLs, or request parameters. This code tricks the database into running unintended commands. As a result, hackers can access, change, or delete sensitive data. Veja tambem: How to Spot Credential Stuffing Attacks: Essential Signs & Defense.
For example, imagine a website login form where users enter their username and password. If the site builds its SQL queries using user input directly, an attacker could type something like ' OR 1=1 -- in the username field. This changes the intended SQL statement, often letting the attacker log in without proper credentials.
In 2026, SQL injection attacks still make global headlines. According to Verizon’s 2025 Data Breach Investigations Report, about 30% of web attacks last year involved some form of injection. Many businesses still rely on old code that does not use proper security practices. Because of this, SQLi remains a prime target for attackers.
Knowing how to recognize signs of this approach helps you close vulnerabilities before they cause damage. Modern attackers use both classic and advanced techniques, so keeping up is essential.
Attackers seek out any point where user input interacts with the database. These can be login forms, search bars, feedback forms, or even custom APIs. Some attackers automate their searches, probing thousands of websites each day to spot weaknesses.
For the ismartfeed.com audience — professionals and enthusiasts keen on digital safety — understanding how to spot these threats is more than a technical skill. It is a business necessity. In fact, a single successful SQL injection attack could expose customer records, payment info, or private messages. This could cause fines, bad press, and loss of trust. Therefore, early recognition is your first line of defense.
Common Symptoms of SQL Injection Attack
There are several classic warning signs that your system may be vulnerable or under attack:
- Unexpected database errors in the browser: Attackers often cause strange SQL errors that reveal database details.
- Sudden changes in website content: If part of your site looks hacked, SQL injection may be to blame.
- Unauthorized data access: Logs may show users accessing records they should not see.
- Log spikes for suspicious input patterns: Repeated use of typical SQLi payloads in request logs is a red flag.
- `’ or ” in input fields
- SQL terms like
SELECT,UNION,DROP - Attempts to include SQL functions:
SLEEP(),CHAR(),CAST()
In summary, recognizing the foundation of SQL injection helps you spot risks early. Next, we will dive deeper into specific signs and attack patterns seen in 2026.
Practical Signs: How to Recognize SQL Injection Techniques in Modern Web Applications
If you want to know how to recognize SQL injection techniques in real time, start by looking for certain patterns in website behavior, logs, and input handling.
Attackers usually start with “probing” — entering strange values into forms, URLs, or API calls. Watch for input like single quotes ('), double quotes ("), semicolons (;), or SQL keywords (SELECT, UNION, DROP). For example, someone might try adding admin' -- as a username.
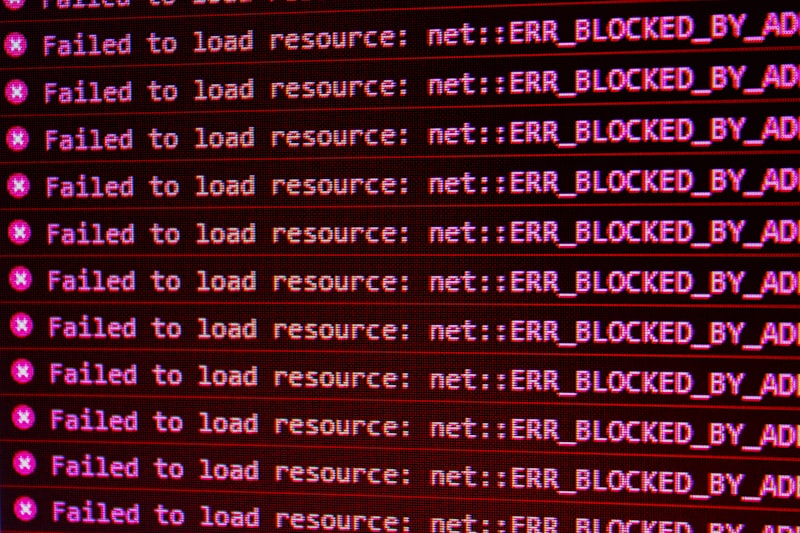
In addition, log files may show repeated errors such as:
` You have an error in your SQL syntax `
or
` Unclosed quotation mark after the character string `
These errors often occur when someone tries to break out of your intended SQL structure.
On the other hand, attackers may use time-based queries to check if their injection works. For instance, they might insert an input like:
` 1′ OR SLEEP(5) — `
If the response time slows down by several seconds, it could mean the database ran a malicious command. This timing technique is a strong sign of both “blind” SQL injection (where error messages are hidden) and general testing activity.
Attackers also use batch queries, chaining several SQL statements together. For example:
` 1; DROP TABLE users; — `
In secure applications, such requests will fail. However, if you observe errors hinting at missing tables or database schema changes, consider whether SQL injection has occurred.
Furthermore, pay attention to unexpected data in returned pages — such as snippets of database content showing up in search results or profile pages. In some cases, attackers use ‘UNION SELECT’ queries to merge unauthorized data into your app’s normal output.
For teams at ismartfeed.com and similar blogs focused on data and security, keeping web application logs and monitoring error rates can help catch these attacks early. Use monitoring tools that flag suspicious patterns. For instance, OWASP ZAP and SQLmap both help detect suspicious input.
Remember, in modern development stacks, attacks may target APIs, mobile apps, or even scripts. Therefore, test all entry points, not just visible forms. In summary, a trained eye combined with the right tools increases your odds of spotting SQL injection early and responding quickly.
Specific SQL Injection Patterns: Examples and Red Flags to Spot
Recognizing SQL injection relies on knowing which patterns attackers use today. Here are several real-world examples and warning signs tailored for the ismartfeed.com audience.
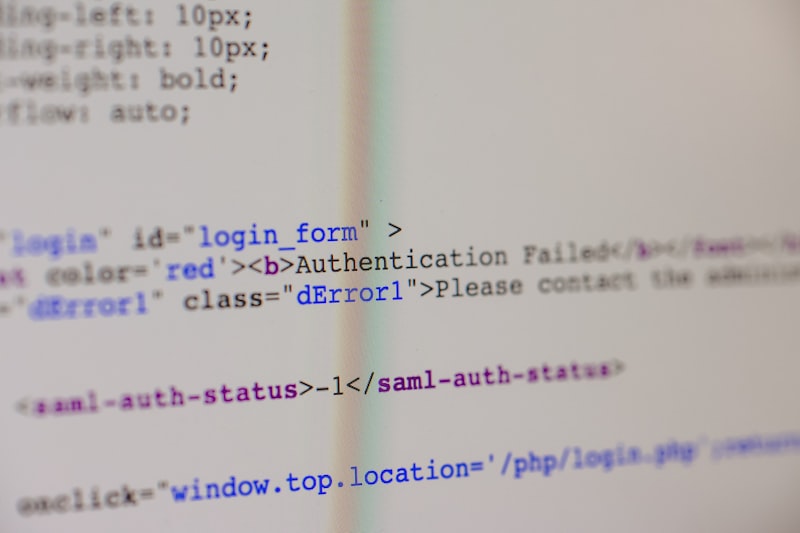
First, let’s look at authentication bypass. If a login form allows “admin’–” as a username (and any password), the system may log in as admin. The SQL query becomes:
`sql SELECT * FROM users WHERE username = ‘admin’–‘ AND password = ‘password’ `
In SQL, anything after -- is a comment, so the password check vanishes. Therefore, any failed login attempts with suspicious usernames or extra symbols are a top concern.
Another classic signal: Successful access to unexpected data after injecting queries like:
` ‘ UNION SELECT username, password FROM users — `
If your application shows login details (or unexpected records) in the results page, you likely have a SQL injection flaw.
Time-based attacks are also common in blind SQLi (where errors are hidden). For example, attackers might try:
` id=5; WAITFOR DELAY ’00:00:10′– `
If the page takes exactly ten seconds for this request, they’re testing response manipulation — a red flag.
Your logs are a goldmine for spotting this approach. Therefore, use filters to catch requests with typical keywords or symbols:
In addition, changes in schema, such as deleted tables or dropped columns, may show someone chained extra statements with a semicolon (;). If this behavior appears, especially after user actions, audit your code immediately.
Consider the following web request:
` http://yoursite.com/item?id=5 OR 1=1 `
If this input shows every item in your database, you have a serious exposure.
Attackers may also encode payloads to bypass input filters. For example, using %27 for a single quote or using concatenation to assemble keywords from characters.
Finally, if your site suddenly leaks internal error messages, stack traces, or table names, it’s a strong sign that someone is prodding for SQL weaknesses.
For digital professionals aligned with ismartfeed.com, regular reviews of code, server logs, and user requests help identify these patterns early. Set up alerts for suspicious input and use automated scanners to stay ahead of threats. In fact, many tools can replay log data and highlight likely SQLi attempts so you can patch or block affected entry points.
Defending Against SQL Injection: Best Practices for Your Site or App
Now that you know how to recognize SQL injection techniques, defense is the next logical step. Keeping systems safe requires both detection and active protection.
First, never trust user input. Always treat anything a user enters as unsafe. For all database queries, use parameterized statements or prepared statements. These methods separate code from data, so input cannot change the query’s structure.
For example, in PHP with PDO:
`php $stmt = $pdo->prepare(‘SELECT * FROM users WHERE username = ?’); $stmt->execute([ $username ]); `
Similarly, in Python with SQLite:
`python cursor.execute(‘SELECT * FROM users WHERE username=?’, (user,)) `
Using these methods blocks most injection attempts, no matter what the attacker tries as input.
Second, keep your software up to date. Many known SQL vulnerabilities were patched years ago, but not all systems use current patches. Updating web servers, application frameworks, and database engines keeps attackers at bay.
Third, validate and sanitize all input. This means checking that user inputs match expected data types, lengths, and patterns. For example, if a field should only have numbers, reject any input with text or symbols.
Fourth, hide detailed error messages from users. Exposing database errors helps attackers refine their input. Therefore, log errors privately — but show generic, nontechnical messages on the website.
Adding a web application firewall (WAF) such as ModSecurity can also block known malicious patterns before they reach your code. Many modern hosting providers offer built-in WAF services for extra protection.
Don’t forget to use least privilege for database accounts. The web app should only have permissions needed for its tasks. For example, if it never deletes tables, remove that right. This keeps any damage from a successful attack as limited as possible.
Finally, scan your website or app often. Tools like OWASP ZAP and SQLmap can run automated tests, simulating attacks and highlighting weaknesses.
For ismartfeed.com readers, adding these habits to daily workflow greatly reduces your risk and helps keep sensitive content safe in 2026.
Training, Monitoring, and Staying Ahead: A Long-Term Approach

Staying safe from injection attacks is not a one-time fix. It requires ongoing vigilance, regular training, and monitoring tailored to your environment.
First, educate your team. Developers, testers, and even support staff should understand the basics of SQL injection. Hold regular workshops or training sessions. For example, show team members how improper string formatting leads to vulnerabilities. Demonstrate real attack examples in a safe, test setting.
Second, create a monitoring plan. Use automated log analysis to alert you to strange patterns of activity. For large organizations or data-driven blogs, dedicated intrusion detection systems (IDS) offer another layer of monitoring. Tailor your alerts to common attack attempts discussed earlier.
Third, stay informed. Cybersecurity threats are always evolving. Follow news from trusted sources like Krebs on Security or OWASP. Join industry groups or online communities focused on web security. Therefore, you’ll be ready to adjust your defenses when new threats appear.
Fourth, review your site’s third-party code and plugins. Many SQL injection vulnerabilities come from outdated or poorly maintained libraries. To minimize risk, audit any plugins, libraries, or open-source packages your site uses. Update or replace risky components early.
Finally, create a response plan. Know what steps to take if a SQL injection attack is detected. For example, have a list of emergency contacts, a process for locking down the site, and instructions for alerting users if their data may be at risk. Document this plan and review it with your team at least twice a year.
Regular security testing, staff training, and smart monitoring mean you’ll spot problems before they escalate. For the ismartfeed.com audience, this approach turns website vulnerabilities into manageable risks — and keeps your data and reputation secure.
Conclusion
In 2026, knowing how to recognize SQL injection techniques is vital for every content creator, developer, and digital business owner. SQL injection remains a serious risk, but spotting early warning signs puts you one step ahead.
Stay alert for odd input patterns, strange errors, and changes in data access. Use strong practices like parameterized queries, careful input validation, and regular automated scans. Train your team and always keep your software up to date.
In summary, understanding these techniques and responses can help protect your blog, web app, or data service from one of the oldest — yet most dangerous — threats online. Take proactive steps now to keep your digital assets and user trust safe all year long.
