If you want to protect your online accounts and data, it is crucial to learn how to spot credential stuffing attacks. This type of cybercrime is on the rise in 2026, affecting millions of users and organizations worldwide.
You may have heard about large data breaches or sudden spikes in login attempts. Often, these are linked to criminals reusing stolen passwords. In fact, credential stuffing is among the top threats in the cybersecurity landscape today.
In this guide, you will find out how these attacks work, clear signs to look for, and smart steps to respond. We will use real examples and offer tips made for both individuals and businesses. Let’s help you stay ahead of the risks on the internet.
What Is Credential Stuffing and Why Does It Matter in 2026?
To understand how to spot credential stuffing attacks, it helps to know what this threat involves. Credential stuffing is when cybercriminals use stolen usernames and passwords (usually from earlier data breaches) to try and break into accounts on other platforms.
For example, imagine you reused the same password on your social media and bank account. If a hacker gets that password from a past leak, they can try it on other sites where you might have an account. In fact, research by Verizon’s Data Breach Investigations Report shows that over 80% of hacking-related breaches involve stolen or reused credentials.
In 2026, credential stuffing remains a leading cause of big security incidents. Attackers use bots to automate thousands of login attempts quickly. Because millions of people reuse passwords, this approach often works.
Credential stuffing is a threat for both individuals and companies. If attackers get in, they can steal sensitive personal data or even empty bank accounts. Plus, businesses may find accounts compromised, which can lead to system downtime, fraud, and reputational harm. In other words, no one is immune to this risk.
Because of this, learning how to spot credential stuffing attacks has become a vital skill for everyone online. In the next sections, we will explore the clear signs to watch for and how you can respond fast.
Real-World Impact
Real cases highlight the threat. In early 2026, a major streaming service suffered a breach affecting over five million user accounts. Investigations found that credential stuffing, not a new hack, was the root cause, using login details bought from the dark web.
Similarly, many small businesses face account takeovers because staff reuse passwords. Therefore, being able to spot these attacks early can prevent costly damages.
Key Signs That Reveal Credential Stuffing Attacks Are Happening

Spotting credential stuffing is not always easy. However, several warning signs can show that this approach is underway. It’s helpful to know both technical signals and patterns in account activity.
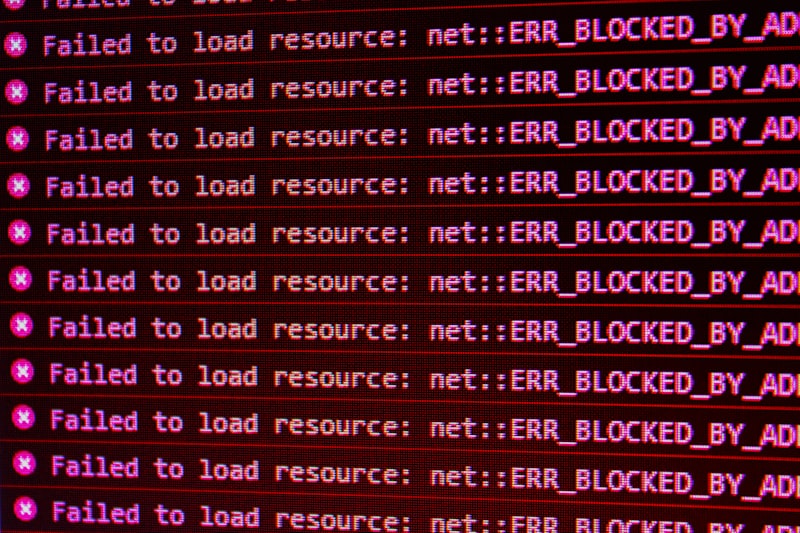
First, monitor for unusual spikes in login traffic. For example, if your website sees thousands of failed logins in minutes, this is a red flag. Most legitimate users will not try to log in so often or fail at that scale.
In addition, attackers often use many different IP addresses to avoid detection. You may see logins coming from countries where you have few or no users. In other words, geographic irregularities in access can indicate trouble.
Next, watch for a sharp increase in “forgot password” requests. Likewise, if many users suddenly complain about account lockouts, something suspicious may be happening.
For businesses, technical logs can show clear patterns. Some common ones are:
- Multiple login attempts from the same device or location in a short time
- Use of automation tools, such as bots, which often leave digital fingerprints
- Failed logins for accounts that have not been used in a long time
- Web Application Firewalls (WAFs): These spot and block suspicious login patterns automatically
- Rate limiting: This limits how many login attempts a user can make in a short time
- IP blocking and geo-fencing: Blocking traffic from unfamiliar countries reduces automated attacks
- Behavioral analytics: These tools “learn” typical user behavior and alert when something changes
- Identity and Access Management (IAM) systems: These systems can force password resets for at-risk accounts
Because credential stuffing often targets a vast number of users, these patterns tend to stand out. You may also hear from users who were locked out of their own accounts or report unauthorized activity. Therefore, monitoring user feedback and help-desk tickets adds another layer of detection.
Finally, if you use security tools or third-party monitoring, they may send you alerts when they see these patterns. In summary, it is the combination of unusual login patterns, geographic anomalies, and user feedback that can help you spot this threat.
Example: Retail Business Facing an Attack
Consider a mid-sized online store in 2026. One evening, the IT team notices 10 times the normal login volume from hundreds of overseas IP addresses. At the same time, users start calling support about locked accounts.
Because of this fast response, they are able to block suspicious traffic and force a password reset before any major damage occurs. This scenario shows why knowing these signs is so important.
Tools and Best Practices for Detecting Credential Stuffing (for Individuals and Organizations)
To better spot credential stuffing attacks, a mix of tools and practical steps is key. Both individual users and organizations have options to boost their defenses.
For individuals, strong password habits are crucial. Using unique passwords for every website prevents attackers from gaining access to multiple accounts with one stolen login. In addition, password managers can create and safely store these unique credentials for you.
Many online services in 2026 now offer two-factor authentication (2FA). This adds a second step to log in, such as a code sent to your phone. Therefore, even if a hacker gets your password, they cannot access your account without that extra proof.
It is also wise to use breach notification services. Websites like Have I Been Pwned let you check if your email or username has been in a data leak. If so, change your passwords and enable 2FA right away.
Organizations can use even more advanced tools. These include:
For example, many banks use device fingerprinting in 2026 to spot strange logins, such as when someone tries to access your account from a new computer for the first time.
In fact, combining several detection strategies is the best way to spot credential stuffing in real time. No single tool is perfect, but together they form a solid defense.
Staff Training
For businesses, staff awareness is essential. Educate employees about safe password practices and how to spot suspicious system notifications. Quick human response often prevents much larger incidents.
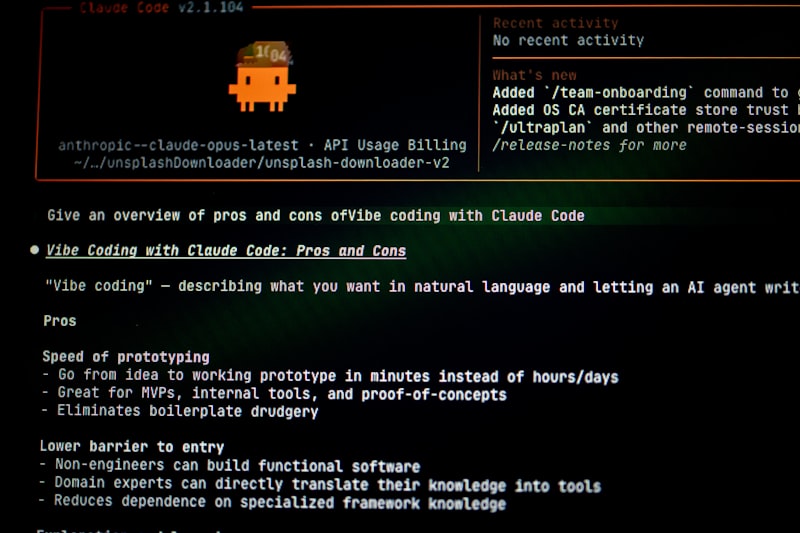
Using Artificial Intelligence
Cutting-edge solutions in 2026 use artificial intelligence to detect credential stuffing attempts. AI systems analyze traffic in real time, learning to flag patterns typical of automated login attacks faster than a human analyst could.
How to Respond Quickly Once Suspecting Credential Stuffing
Once you spot possible credential stuffing, act fast to limit damage. Time is everything in these cases. The right response steps vary a bit for individuals and organizations.
First, if you are an individual and suspect your account was targeted, change all passwords linked to your email. In addition, enable two-factor authentication on all accounts where it is available. Doing so blocks most future attacks, even if the attacker has your password.
Look at your recent account activity for any signs of unusual activity. For example, check for new devices or unfamiliar transactions. Report anything suspicious to the platform’s support team. In summary, speed and vigilance limit harm.
Businesses need a plan for these situations. First, block suspicious login attempts, often using WAF or rate-limiting features. Next, force a password reset for users whose accounts were hit by the attack. In addition, notify affected customers quickly. This helps keep trust and may even be required by law.
Audit your systems to see if any attackers got deeper access. For example, review logs and check for unusual admin activity or data exports. Consult with your cybersecurity team or external experts to assess the need for further steps.
Legal and Regulatory Considerations
In 2026, many regions have strict rules to report data breaches. If you find evidence that personal data was accessed, make sure to follow your area’s regulations. For more details, you can see guidelines at CISA.
Invest in user education as well. Share updates with your users or staff about why unique passwords and 2FA matter. In addition, consider running regular drills to prepare for these attacks.
Business continuity matters, so update your incident response playbooks with lessons learned from each case. In other words, never let an attack pass without making your processes stronger.
Long-Term Security Improvements
Responding to a single event is only part of the challenge. Use what you learn from each attack to fix weak spots. For example, some companies move logins behind a secure portal or add risk-based authentication to flag unlikely logins.
In fact, the best way to fight credential stuffing over time is to reduce password reuse and build a culture of security awareness.
Conclusion
In summary, knowing how to spot credential stuffing attacks can protect both your personal accounts and your organization. Watch for spikes in login failures, odd geographic access patterns, and user complaints about locked accounts. Use tools like password managers and two-factor authentication to reduce risk.
For businesses, combine web firewalls, behavioral analytics, and staff training for the best line of defense. Act fast if you spot signs of this threat. Always update your response plan based on new challenges.
Staying alert and ready in 2026 is not optional—it is the only way to keep data and systems safe. Start with the steps above to give yourself or your company the best protection against this growing cybercrime.
